Dublin's IFSC
About the IFSC
This year the IFSC celebrates it's 37th year as one of the world's leading financial services centres. The importance of the International Financial Services Centre to the Irish economy is indisputable. It has become one of the leading hedge fund service centres in Europe, and many of the world's most important financial institutions have a presence here.
About IFSCBusiness Directory Companies & Services
The IFSC directory is an easy-to-use index of all the services you're ever likely to need if you live or work in or around the IFSC & Docklands area.
Featured News
Upcoming Events
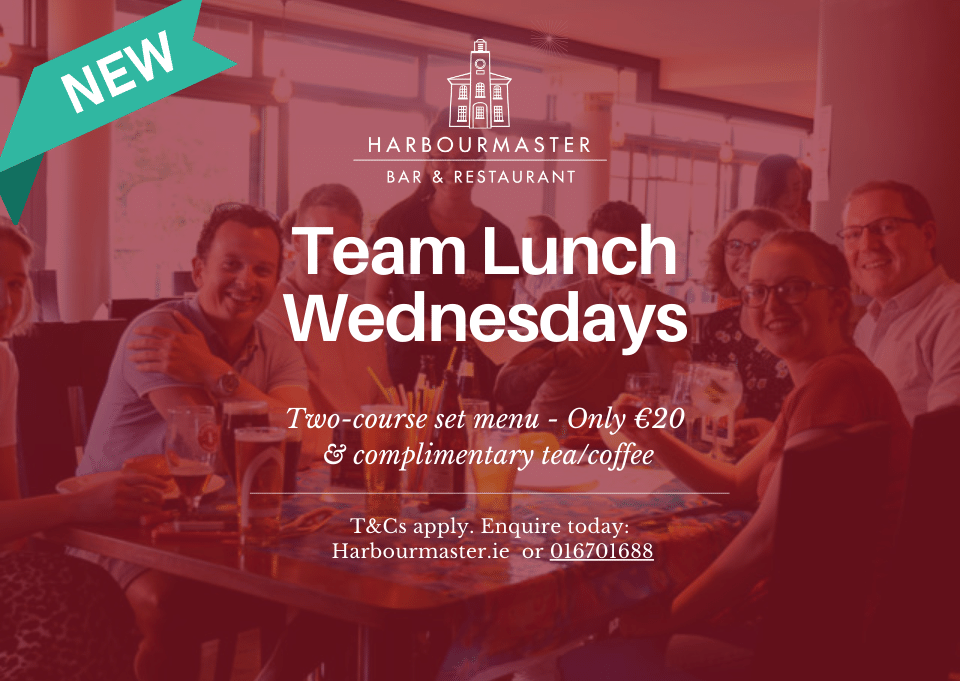
Special Offers
Find unique experiences, weekend breaks, restaurant deals. Get exclusive discounts on services and much more. Buy and book online. New offers are added daily!
View all ADD A SPECIAL OFFER